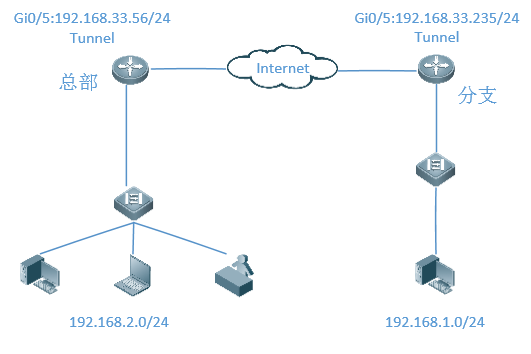
一、组网需求
保护总部与分支子网之间的IP数据通信,通过隧道建立连接,并对数据进行加密,保证安全,GRE ovre IPSEC 的原理是用户业务数据封闭到GRE隧道,GRE隧道的数据再被ipsec加密,所以配置ipsec感兴趣流时,源地址和目标地址为两端路由器的外网接口的IP地址;
二、组网拓扑
三、功能原理
采用GRE建立隧道,实现内网间的通信,使用ipsec对总部与分支间的隧道流量进行加密
四、配置要点
1、本配置是建立在NBR-E已经正确完成了快速配置的基础之上的;
2、配置routeA(总部)为GRE over ipsec服务器端;
3、配置routeB(分支)为GRE over ipsec客户端;
4、两端的参数要保持一致
GRE Tunnel的隧道的源目的地址要相互对应
认证方式:预共享密钥,密钥为ruijie
IKE算法:3DES-MD5,DH2
IPSec协商交互方案:esp(3des-md5)
五、配置步骤
Web上还不支持GRE隧道的配置,只能在CLI下配置
1.总部
1)、配置ipsec第一阶段
crypto isakmp enable
crypto isakmp policy 1
encryption 3des
authentication pre-share
hash md5
group 2
2)、配置预共享密钥和变换集合
crypto isakmp key 0 ruijie address 192.168.33.235
crypto ipsec transform-set myset esp-3des esp-md5-hmac
mode transport
3)、配置感兴流
ip access-list extended 199
10 permit gre host 192.168.33.56 host 192.168.33.235
4)、定义一个加密映射集合
crypto map mymap 1 ipsec-isakmp
set peer 192.168.33.235
set transform-set myset
match address 199
5)、在接口上调用加密图
interface GigabitEthernet 0/5
ip address 192.168.33.56 255.255.255.0
crypto map mymap
6)、配置GRE的Tunnel接口
interface tunnel 1
tunnel source 192.168.33.56
tunnel destination 192.168.33.235
ip address 2.2.2.1 255.255.255.0
7)、配置路由
ip route 192.168.1.0 255.255.255.0 tunnel 1
ip route 0.0.0.0 0.0.0.0 192.168.33.1 #192.168.33.1为外网网关
2.分支
1)、配置ipsec第一阶段
crypto isakmp policy 1
encryption 3des
authentication pre-share
hash md5
group 2
2)、配置预共享密钥和变换集合
crypto isakmp key 0 ruijie address 192.168.33.56
crypto ipsec transform-set myset esp-3des esp-md5-hmac
mode transport
3)、配置感兴流
ip access-list extended 199
10 permit gre host 192.168.33.235 host 192.168.33.56
4)、定义加密映射
crypto map mymap 1 ipsec-isakmp
set peer 192.168.33.56
set transform-set myset
match address 199
5)、在接口上调用加密图
interface GigabitEthernet 0/5
ip address 192.168.33.235 255.255.255.0
crypto map mymap
6)、配置GRE的Tunnel接口
interface tunnel 1
tunnel source 192.168.33.235
tunnel destination 192.168.33.56
ip address 2.2.2.2 255.255.255.0
7)、配置路由
ip route 192.168.2.0 255.255.255.0 tunnel 1
ip route 0.0.0.0 0.0.0.0 192.168.33.1 #192.168.33.1为外网网关
六、配置验证
1.查看ipsec状态
zongbu#show crypto state
destination source state st-id pa-st mapid mode ir lifetime
192.168.33.235 192.168.33.56 IKE_IDLE 1 0 1 9 1 85948
2.查看隧道流量
zongbu#show crypto ipsec sa
Interface: Tunnel 1
Profile map tag:profile-map
==================================
sub_map type:profile, seqno:0, id=1
local ident (addr/mask/prot/port): (192.168.33.56/0.0.0.0/47/0))
remote ident (addr/mask/prot/port): (192.168.33.235/0.0.0.0/47/0))
PERMIT
#pkts encaps: 4861, #pkts encrypt: 4861, #pkts digest 4861
#pkts decaps: 0, #pkts decrypt: 0, #pkts verify 0
#send errors 235, #recv errors 0
Inbound esp sas:
spi:0x34ef2301 (888087297)
transform: esp-3des esp-md5-hmac
in use settings={Transport Encaps,}
crypto map profile-map 0
sa timing: remaining key lifetime (k/sec): (4606445/3143)
IV size: 0 bytes
Replay detection support:Y
Outbound esp sas:
spi:0x10c2d27a (281203322)
transform: esp-3des esp-md5-hmac
in use settings={Transport Encaps,}
crypto map profile-map 0
sa timing: remaining key lifetime (k/sec): (4606445/3143)
IV size: 0 bytes
Replay detection support:Y